How to Understand Net Neutralization and Its Benefits

- Introduction to Net Neutralization
- The Concept of Neutrality in the Internet
- Historical Context of Net Neutrality
- How Net Neutralization Works
- Benefits of Net Neutralization
- The Impact on Businesses and Content Creators
- Current Challenges to Net Neutralization
- Global Perspectives on Net Neutrality
- Future Outlook for Net Neutralization
Introduction to Net Neutralization
Net neutralization refers to the principle that all internet traffic should be treated equally, without discrimination regarding content, platform, user, or application. This concept posits that service providers must not favor any specific data, thereby preserving an open and fair online environment. The practice of net neutralization is essential for maintaining the transparency and integrity of the internet, allowing users to access and share information freely while preventing potential monopolistic practices by internet service providers (ISPs).
The core tenet of net neutralization asserts that ISPs should not engage in practices such as throttling, prioritizing service, or blocking access to certain websites or applications. This neutrality ensures a level playing field, where both small startups and large corporations can compete on equal terms. A lack of net neutralization may lead to situations where larger entities dominate the market, as they could afford to pay ISPs for faster access, ultimately silencing smaller voices.
Moreover, the implications of net neutralization extend far beyond individual users to encompass the broader online ecosystem, including content creators, businesses, and educators. Without net neutralization, the potential for innovation and diversity in online content diminishes, hindering social and economic growth. Users rely on accessible internet services to engage in research, learning, and creation. Therefore, understanding net neutralization’s importance is crucial for advocating policies that protect user rights and foster an inclusive digital landscape.
In sum, net neutralization serves as a foundational principle that reinforces the idea of an equitable internet. By maintaining this neutrality, we encourage an environment where creativity, diversity, and accessibility are upheld, reflecting the democratic values that the internet was initially built upon.
The Concept of Neutrality in the Internet
Net neutrality refers to the principle that internet service providers (ISPs) must treat all data on the internet equally, without discriminating or charging differently by user, content, website, platform, application, or method of communication. This foundational concept ensures that ISPs cannot favor certain content or applications over others, thereby maintaining a level playing field for all online services. Under net neutrality, all internet traffic should be regarded equally, which restricts ISPs from blocking, throttling, or prioritizing specific services.
The significance of net neutrality extends beyond technical definitions; it is vital for fostering innovation, competition, and free expression online. When ISPs are prohibited from manipulating internet traffic, startups and smaller companies have equal opportunities to compete with established firms. Without such a principle, large corporations could prioritize their services or those of partners, potentially stifling competition and limiting consumer choices. This could result in a digital landscape that favors only well-funded entities, leaving smaller or emerging businesses struggling to reach their audiences.
Moreover, neutrality in the internet facilitates access to diverse content for all users. With an equitable system, individuals from various backgrounds can access the same information and services, which is crucial for educational and social equality. The absence of net neutrality could lead to a tiered internet, where wealthier users enjoy faster access and superior services, thereby creating a digital divide. Thus, the principles of net neutrality are not just about the technical operation of the internet; they also have broader implications for democracy, human rights, and equitable access to information, which highlight its crucial role in today’s society.
Historical Context of Net Neutrality
Net neutrality, a term that encapsulates the principle of treating all internet data equally, has a history that reflects the evolving relationship between technology, policy, and society. The roots of net neutrality can be traced back to the early days of the internet when it was predominantly a research tool. In 1996, the Telecommunications Act represented a significant legislative effort in the United States aimed at fostering competition and innovation. While this act laid the groundwork for broadband expansion, it did not explicitly address net neutrality, which would become a pivotal issue in the years to come.
In 2005, then-FCC Chairman Kevin Martin asserted the necessity of net neutrality principles, stressing that internet service providers (ISPs) should not discriminate against competing services or applications. However, it was not until 2010 that the Federal Communications Commission (FCC) established formal rules to protect net neutrality. These rules were aimed at preventing ISPs from blocking or throttling lawful content, applications, and services, laying the groundwork for an open internet.
The momentum for net neutrality gained considerable traction following a pivotal 2014 court decision in Verizon v. FCC, which struck down the FCC’s broader authority to enforce net neutrality rules. This decision prompted widespread public engagement and advocacy for stronger net neutrality protections, resulting in the FCC’s 2015 decision to reclassify broadband internet under Title II of the Communications Act, thereby affording it enhanced regulatory provisions.
Despite these advancements, the battle for net neutrality continues to evolve. In 2017, the FCC voted to repeal the 2015 regulations, igniting renewed debates among stakeholders, including ISPs, content providers, and consumer advocacy groups. Events such as these underscore the historical complexity surrounding net neutrality and illustrate how it remains a critical topic in discussions regarding internet governance, regulation, and the ongoing quest for equitable access to digital information.
How Net Neutralization Works
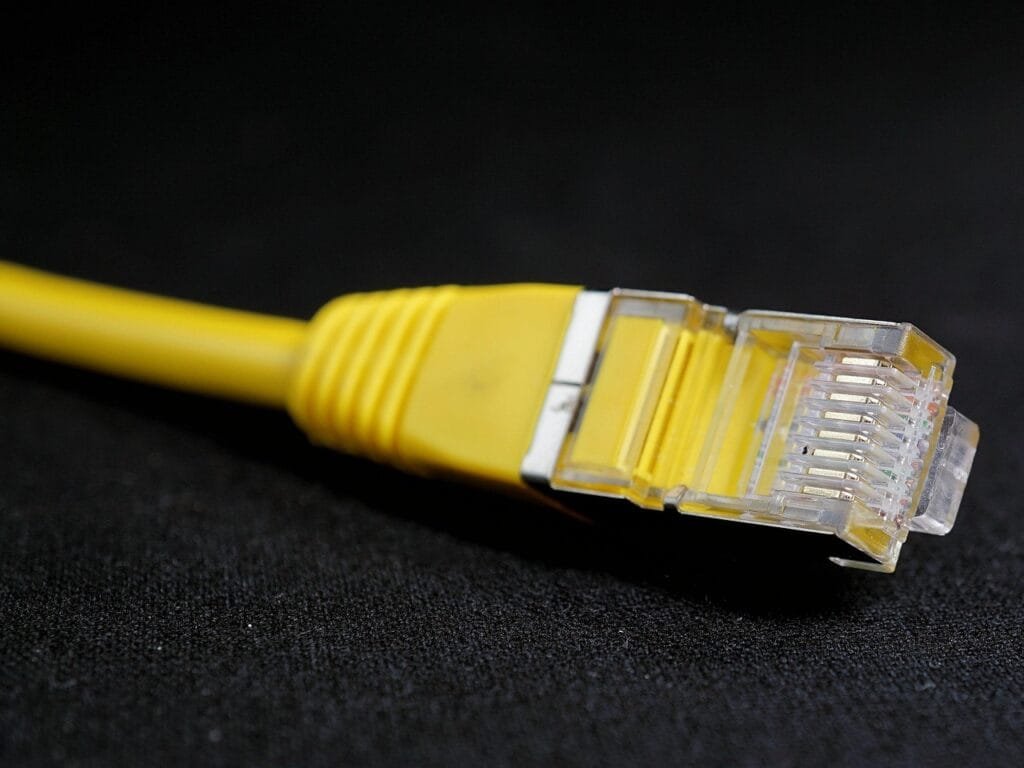
Net neutralization, a principle designed to maintain equal access to internet services, operates through a combination of regulatory frameworks, technologies, and methodologies. At its core, net neutralization assures that all data packets are treated uniformly, regardless of their source or destination. This principle is upheld by various laws and regulations established by governmental and independent bodies that aim to prevent favoritism among internet traffic.
Regulatory frameworks on net neutralization have evolved to impose requirements on internet service providers (ISPs) to refrain from discriminating against specific content, applications, or services. For instance, in the United States, the Federal Communications Commission (FCC) has implemented rules to protect against blocking, throttling, and paid prioritization of internet traffic. These regulations are essential in fostering an open internet where users can access content freely without ISP interference.
Technologically, net neutralization is enforced through a series of protocols and mechanisms. Traffic management practices employed by ISPs are regulated to ensure they do not intentionally degrade service for particular websites or applications. Technologies like deep packet inspection (DPI) and bandwidth throttling are prohibited if used unfairly, serving to uphold net neutralization principles. Furthermore, peering agreements between ISPs and content providers are structured to ensure equal treatment, promoting competitive access to services at similar speeds and qualities.
Methodologies employed in net neutralization involve continuous monitoring and transparency measures. Independent organizations and regulatory bodies frequently assess ISP practices to ensure compliance with net neutrality rules, often relying on input from advocacy groups and the public. By mitigating unfair practices in the digital ecosystem, net neutralization ultimately champions consumer rights and fosters innovation across diverse online platforms.
Benefits of Net Neutralization
Net neutralization, the principle that Internet service providers (ISPs) must treat all data on the Internet equally, presents several significant benefits that contribute to a thriving digital ecosystem. Primarily, it promotes innovation, as it allows startups and small companies to compete on a level playing field with larger corporations. Without net neutralization, ISPs could prioritize their own services or those of businesses that pay higher fees, limiting the ability of new entrants to reach consumers effectively. For instance, platforms like YouTube and Netflix are products of an environment where all websites receive equal treatment, enabling diverse services to flourish without ISPs placing barriers to entry.
Another critical advantage of net neutralization is the protection of consumer rights. By ensuring that all Internet users have unfettered access to content and applications, consumers are empowered to make choices regarding the information they consume. This degree of freedom prevents ISPs from engaging in unfair practices, such as throttling or blocking certain websites, effectively maintaining an open Internet for everyone. For example, in regions where net neutralization is enforced, consumers have reported greater satisfaction with their Internet services, as they can access content without arbitrary limitations imposed by ISPs. This practice fosters an environment where users can freely engage with diverse viewpoints and resources.
Moreover, net neutralization ensures a fair and competitive marketplace. With equal access to broadband networks, businesses are not coerced into paying for preferential treatment, which fosters healthy competition. This competitive environment incentivizes companies to innovate and improve their services continuously. Companies like Spotify and Airbnb have been able to thrive and disrupt traditional markets precisely because of a level playing field that net neutralization facilitates. In this way, net neutralization does not just protect individual interests; it enhances the overall health of the economy by supporting a vibrant and varied online marketplace.
The Impact on Businesses and Content Creators
Net neutrality has established itself as a critical principle in the realm of the internet, profoundly influencing how businesses, particularly startups and small enterprises, and individual content creators operate. By ensuring that all data transmitted over the internet is treated equally, net neutrality allows businesses of all sizes to compete on an even playing field. This accessibility is essential for startups seeking to gain traction in their respective markets, as they often operate with limited resources. Without the constraints imposed by internet service providers (ISPs), startups can launch their products and services without the fear of preferential treatment afforded to larger corporations.
Moreover, net neutrality fosters innovation and creativity. Content creators can share their work freely, thereby enriching the digital ecosystem and providing diverse options for consumers. This environment enables individuals to reach audiences they may not have been able to access under a tiered service model. For instance, a small video production company can distribute content just as effectively as a larger competitor, ensuring that unique voices and ideas can emerge without undue barriers. The resulting diversity not only enhances consumer choice but also promotes the overall health of the digital marketplace.
However, while net neutrality presents numerous opportunities, it is not without its challenges. Startups still face hurdles such as limited visibility in a crowded market and the necessity of ongoing investment in marketing and technology. Additionally, without regulations, the risk of ISPs prioritizing certain content for financial gain could emerge, leading to potential inequalities that disadvantage smaller enterprises and independent creators. Therefore, the ongoing discourse around net neutrality remains vital in assessing how it can be upheld to ensure that all participants in the digital landscape can thrive and contribute effectively to the economy.
Current Challenges to Net Neutralization
In recent years, net neutrality has faced an array of challenges that threaten to undermine its fundamental principles. One significant challenge arises from legislative changes within various jurisdictions. Governments have debated and, in some cases, enacted laws that either repeal existing net neutrality regulations or weaken their enforcement, impacting the free flow of information on the internet. The repeal of net neutrality regulations in the United States is a notable example, illustrating how electoral politics can significantly affect the state of internet accessibility and fairness.
Corporate lobbying is another critical factor contributing to threats against net neutrality. Large internet service providers (ISPs) often advocate for policies that benefit their business models, pushing for deregulation that may allow them to control bandwidth allocation. This influence can result in a tiered internet system where companies prioritize their services over competitors, ultimately harming smaller entities and stifling innovation. Such lobbying efforts create a challenging landscape for advocacy groups striving to preserve net neutrality in the face of corporate interests.
Technological advancements also pose challenges to net neutrality. The increasing reliance on data-intensive services, such as streaming and online gaming, places significant demands on internet infrastructure. ISPs may argue that they require the ability to manage traffic to ensure consistent service quality for all users. This position can be seen as a justification for deviating from net neutrality principles, as it raises questions about whether prioritized service delivery could ultimately lead to Internet behaviours that mirror the very biases net neutrality aims to eliminate.
The convergence of these challenges—legislative changes, corporate lobbying, and technological demands—creates a complex environment where the future of net neutrality hangs in the balance. It requires ongoing vigilance from both policymakers and the public to ensure an internet that remains open and accessible for all.
Global Perspectives on Net Neutrality
Net neutrality, the principle that internet service providers must treat all data on the internet equally, has garnered varying responses around the globe. Different countries have adopted distinct approaches to net neutrality, reflecting their unique political, economic, and cultural contexts. An analysis of international perspectives reveals a spectrum of regulations and legal frameworks that shape the environment of internet access.
In the United States, net neutrality has been a contentious issue, characterized by a cycle of regulations and deregulations. The Federal Communications Commission (FCC) established strong net neutrality rules in 2015 under the Obama administration, which prohibited internet service providers from blocking or throttling content. However, these regulations were repealed in 2017, leading to a heated debate over the implications for consumers and innovation. Proponents argue that a lack of net neutrality could result in a tiered internet, favoring larger corporations over small enterprises, potentially stifling competition and harming new startups.
Conversely, the European Union has maintained a more unified stance on net neutrality through its Telecommunications Single Market Regulation. This framework, implemented in 2016, enshrines the right to open internet access, mandating that internet service providers refrain from discriminatory practices. The EU’s approach reflects a commitment to preserving a competitive digital environment, enhancing consumer protection, and fostering innovation across member states.
In contrast, countries like India have embraced strict measures supporting net neutrality. The Telecom Regulatory Authority of India (TRAI) imposed a ban on differential pricing of data services in 2016, ensuring that all users have equal access to internet resources. This proactive approach has been praised for safeguarding the interests of consumers and fostering an inclusive online ecosystem.
As countries navigate the complexities of net neutrality, it becomes evident that approaches vary widely. Each regulatory framework highlights diverse philosophies regarding the role of government, the importance of equitable access, and the future of internet innovation. Understanding these global perspectives is essential for fostering informed discussions and potential collaborations on net neutrality.
Future Outlook for Net Neutralization
The future outlook for net neutrality is inevitably intertwined with the rapid advancement of technology, the evolving political landscape, and shifting societal expectations regarding internet access. As we progress deeper into the digital age, the principles of net neutrality remain a crucial topic of discussion. One prominent trend is the increasing push for legislation that aims to safeguard net neutrality, particularly as public awareness grows about the potential threats posed by the prioritization of certain online content.
Technological advancements, particularly in telecommunications infrastructure, may also impact net neutrality. The rollout of 5G technology and the expansion of broadband access could create scenarios where internet service providers (ISPs) might exploit these advancements to favor certain services over others. For instance, while faster connectivity can enhance user experience for all, there is a risk of ISPs implementing tiered service levels that may compromise the core tenet of net neutrality. Advocates must remain vigilant and proactive to ensure that the internet ecosystem remains level for all users and content providers.
Politically, the fate of net neutrality will heavily depend on the prevailing government policies and public interest advocacy. Various stakeholders, including tech companies, consumer rights organizations, and government bodies, must collaborate to create balanced regulations that promote fair competition and protect consumers. As various jurisdictions approach net neutrality differently, the global landscape may bring forth competing frameworks, influencing international relations among countries regarding internet governance.
Lastly, societal factors such as increasing digital literacy and the demand for equitable access to information will continue to shape the net neutrality debate. A well-informed populace will be pivotal in influencing policy decisions that protect the open internet. As we navigate the complexities of the future, it is crucial to consider the widespread implications of net neutrality in a continually evolving environment, fostering a more inclusive digital society.